Claim leakage in health insurance is any avoidable overpayment that escapes the claims process due to billing errors, provider fraud, document forgery, or system failures, rather than intentional policyholder deception. Industry benchmarks consistently place leakage at 5 to 10 percent of total claims spend. For a TPA processing $200 million in annual claims, that represents $10 to $20 million leaving the system unchallenged every year.
Why Claim Leakage Is the Silent Drain on TPA Profitability
Claim leakage in health insurance bleeds 5 to 10 percent from a TPA’s annual claims spend through errors and fraud that manual audits catch only after settlement. The earlier leakage is detected in the claims cycle, the lower the recovery cost.
Most finance heads and COOs know their loss ratio. Far fewer can tell you their leakage ratio. That gap exists because leakage hides in the operational machinery of the claims lifecycle: inside billing codes, document metadata, drug quantities, and provider history. It does not announce itself. A claim for an ICU admission when a patient was treated in a general ward looks routine unless someone checks.
The Reinsurance Group of America’s 2024 Global Claims Fraud Survey, which drew 60 percent of its respondents from the Asia-Pacific region, found that 74 percent of insurers report fraud cases are holding steady or rising. One in 30 claims globally shows signs of fraudulent activity. When fraud is suspected, the average investigation cycle stretches from three weeks to 68 days.
Every rupiah, ringgit, or rupiah paid on a leaky claim is a permanent loss. Post-settlement recovery rates in APAC health insurance hover below 20 percent.
The business case for front-loading detection is simple: catching leakage before settlement is always cheaper than recovering overpayments after.
The Five Types of Claim Leakage That Hit APAC TPAs Hardest
The five main types of claim leakage in health insurance are duplicate billing, upcoding, phantom services, prescription fraud, and document forgery. Each requires a different detection method and carries a different cost signature.
Duplicate Billing
Duplicate billing occurs when the same service or claim is submitted more than once, often with slight variations in date, provider code, or reference number to avoid simple deduplication filters. In high-volume TPA environments processing thousands of claims daily, these slip through manual review. The detection signal is a match on patient ID, procedure code, and service date within a configurable lookback window.
Upcoding
Upcoding is the practice of billing for a more expensive procedure or diagnosis than was actually performed. A laparoscopic procedure billed at open-surgery rates is a classic example. In India’s private hospital network, upcoding treatments by changing disease codes is a documented pattern, identified in a Deloitte Insurance Fraud Survey (2023) in which 60 percent of Indian insurers reported a steady increase in health fraud. The detection signal is a mismatch between the billed code’s expected cost and the clinical documentation in the discharge summary.
Phantom Services
Phantom billing means charging for services that were never rendered. Indonesia’s Corruption Eradication Commission (KPK) launched a massive hospital audit in 2024 after finding phantom billing in JKN-affiliated facilities, with fraud across three hospitals reaching IDR 35 billion. The detection signal is the absence of matching clinical documentation for a billed line item.
Prescription Fraud
Prescription fraud appears as drug quantities that exceed clinical norms, off-formulary drugs submitted under generic codes, or prescriptions that lack a matching diagnostic code. Indonesia’s pharmacy channel is a known hotspot within the national JKN program. Detection requires cross-referencing dispensed quantities against treatment protocols and formulary rules.
Document Forgery
Document forgery ranges from altered discharge dates and changed procedure codes on legitimate documents to entirely fabricated bills. A Deloitte survey reported that the Insurance Institute of India estimates annual losses of Rs 600 to 800 crore from fraudulent healthcare claims, with forged documents a significant contributing factor. AI document authenticity checks examine metadata, font consistency, and structural anomalies that a human reviewer would miss.
Leakage-Type Detection Matrix
| Leakage Type | Detection Signal | APAC Hotspot | AI Gate | Risk Level |
|---|---|---|---|---|
| Duplicate Billing | Same procedure code, patient ID, service date across submissions | India, Malaysia | Gate 1 completeness check | High |
| Upcoding | Diagnosis code vs. billed cost mismatch; contradicts clinical notes | India (private hospitals) | Gate 2 billing extraction | Very High |
| Phantom Services | Billed line item has no clinical documentation match | Indonesia (JKN network) | Gate 2 + HITL review | Very High |
| Prescription Fraud | Drug quantity exceeds protocol norm; off-formulary items | Indonesia (pharmacy) | Gate 2 cross-reference | High |
| Document Forgery | Metadata anomalies, font inconsistencies, altered dates | Malaysia, India | Gate 1 document authenticity | High |
APAC-Specific Leakage Patterns: India, Indonesia, and Malaysia
India’s dominant leakage pattern is upcoding and inflated hospital bills in private cashless networks. Indonesia sees phantom billing in JKN-affiliated facilities. Malaysia’s TPA disputes cluster in GP claims under managed care schemes.
Each market has a distinct fraud topology, which means a single detection ruleset cannot serve all three.
In India, IRDAI’s annual report for FY2024-25 recorded Rs 30,000 crore in rejected or repudiated health insurance claims, a 15 percent jump from the prior year. The Ayushman Bharat scheme alone saw 3.56 lakh fraudulent claims worth Rs 643 crore rejected in FY2024, with 1,114 hospitals de-empanelled for involvement.
In APAC, the problem is not that fraud is hard to find. It is that the manual infrastructure catches it too late, and too rarely, to prevent the overpayment from leaving the system.
In Indonesia, the JKN program covers 82 percent of the population but has run persistent deficits partly driven by fraud. A narrative literature review published in October 2024 confirmed that fraud prevention frameworks remain inconsistently applied across facilities.
In Malaysia, ProtectHealth Corporation, acting as TPA for the Madani Medical Scheme, identified RM 1.5 million in disputed claims from panel GPs by mid-2024, with over 200 private clinics audited or investigated.
The Cost Architecture of Claim Leakage for Health TPAs
A TPA handling $200 million in claims annually loses $10 to $20 million to leakage at the industry average of 5 to 10 percent. The hidden cost multiplier is the 68-day investigation cycle, which inflates operating expenses beyond the initial overpayment.
The Regure claims leakage benchmark places leakage at 5 to 10 percent of total claims spend. For a carrier paying $500 million in annual claims, that is $25 to $50 million in avoidable payments. APAC TPAs face compounded exposure from high claim volumes, fragmented hospital networks, and variable document standards across markets.
According to Deloitte’s 2024 analysis, soft fraud, which includes claim inflation and upcoding, accounts for 60 percent of all fraud incidents but carries a detection rate of only 20 to 40 percent with conventional methods. The most common leakage type is also the hardest to catch manually.
AI-driven detection systems can reduce fraudulent claim payouts by 20 to 40 percent, according to Accenture research cited in 2024 industry analyses. Applied to a $200 million claims book with a 7 percent leakage rate, that represents a recoverable $2.8 to $5.6 million annually.
Architecture: The Two-Gate AI Claims Pipeline
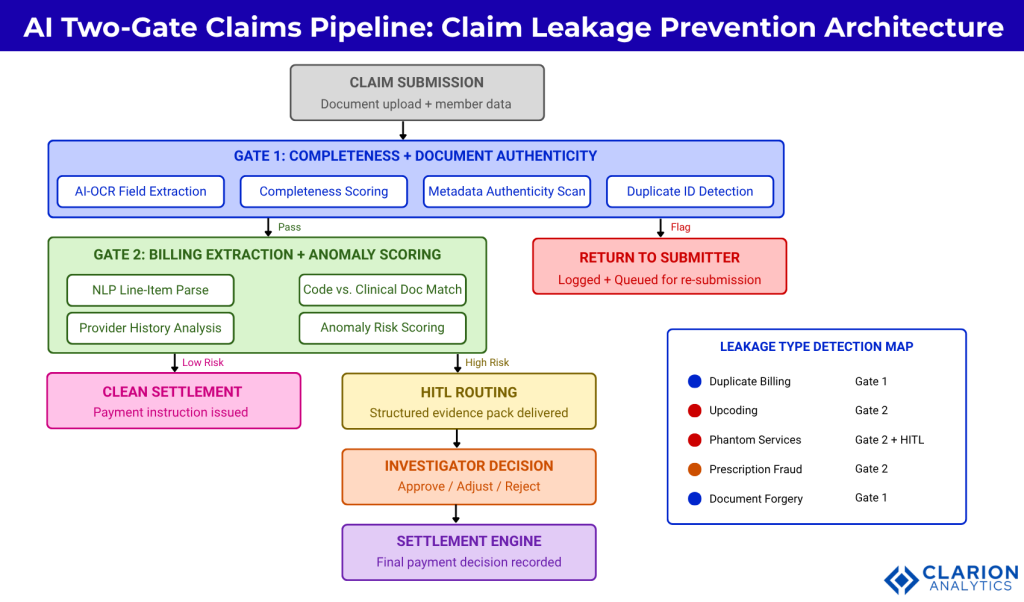
Figure 1: The two-gate AI pipeline intercepts leakage at submission (Gate 1) and at line-item extraction (Gate 2) before any payment instruction reaches the settlement engine. Gate 1 handles completeness and document authenticity checks. Gate 2 applies NLP extraction and anomaly scoring to every billing line. HITL routing sends anomalies above a configurable risk threshold to a human investigator with a structured evidence package. Claims that pass both gates without escalation proceed directly to settlement.
Gate 1: Completeness Check: Stopping Submission Leakage at the Door
Gate 1 uses AI-OCR and document authenticity checks to confirm every required field is present, every document is unaltered, and every submission meets policy eligibility criteria before the claim enters adjudication. This single step prevents a large share of duplicate billing and forgery leakage.
In practice, TPA teams building this layer typically find that 15 to 25 percent of incoming claims have at least one completeness issue: a missing discharge summary, an unreadable prescription, or a policy number that does not match the member record. Without Gate 1, these submissions enter adjudication and stall mid-process, creating both delay and exposure.
Gate 1 components include AI-OCR extraction to pull structured fields from unstructured documents, completeness scoring against a configurable checklist by claim type, metadata validation for document authenticity, and hash-based duplicate detection across a rolling claims history window.
Sprout.ai’s platform describes this intake and triage layer as extracting, codifying, and enriching data from unstructured inbound documents with exceptional speed and accuracy. Their deployment with AdvanceCare, a TPA that processed over one million claims through the AI platform in a single year, cut processing times to 60 seconds for certain claim types while increasing automation rates by more than 10 percent.
Gate 1 is the cheapest point in the claims lifecycle to catch leakage. Stopping a forged document at submission costs a fraction of recovering an overpayment after settlement.
Gate 2: Extraction and Billing Discrepancy Detection
Gate 2 applies NLP and anomaly detection models to every line item in a claim, cross-referencing billed codes against clinical documentation, treatment norms, and provider history. Billing discrepancies are scored and routed to HITL investigators before any settlement instruction is issued.
This is where upcoding, prescription fraud, and phantom services are caught. The NLP models parse diagnosis codes, procedure codes, drug codes, and quantities from unstructured clinical notes and compare them against what has been billed. When a claim charges for an ICU stay but the discharge summary describes a general ward admission, Gate 2 scores that discrepancy and escalates it.
Research published in BMC Medical Informatics and Decision Making (2024) demonstrated that combining association rule mining with unsupervised anomaly detection outperforms single-technique approaches. The CBLOF technique achieved the highest silhouette score of 0.114 in clustering known fraud patterns.
A second 2024 study in Heliyon proposed a multi-channel heterogeneous graph approach that captures relationships between patients, providers, and billing codes simultaneously, outperforming traditional pattern-matching for evolving fraud tactics. For APAC TPAs managing large hospital networks, a single upcoding provider often affects hundreds of claims.
Provider history is factored at Gate 2. A provider whose billing patterns deviate significantly from peers in the same specialty and geography generates a persistent risk signal, not just a single flag.
Detection Approach Comparison
| Detection Approach | Key Strength | Best Used When |
|---|---|---|
| Manual claims audit | Deep contextual judgment on complex cases | Post-settlement recovery; regulatory dispute resolution |
| Rule-based detection engine | High-speed processing; zero latency for known patterns | Enforcing known billing rules and policy exclusions at scale |
| AI Gate 1 (OCR + authenticity) | Catches forgery, duplicates, and incomplete submissions before adjudication | All inbound claims; highest ROI when fraud volume is high |
| AI Gate 2 (NLP + anomaly scoring) | Detects upcoding, phantom billing, and prescription fraud at line-item level | Complex claim types; multi-provider hospital networks |
| HITL routing with AI evidence packs | Combines AI detection accuracy with human expert judgment | High-value claims; ambiguous anomalies requiring clinical expertise |
HITL Routing: Where AI Judgment Meets Human Oversight
HITL routing sends high-risk-scored claims to specialist reviewers with a structured evidence pack generated by the AI, including the anomalous line items, comparable benchmarks, and a suggested action. This design keeps average investigation time under 20 minutes per case.
The common objection from TPA leadership is that HITL routing creates a bottleneck. In practice, the opposite is true. Before AI-assisted routing, an investigator might review an entire claim file to identify the relevant anomaly. With HITL routing, the AI delivers the specific line items that triggered the flag, the benchmark against which they were scored, the provider’s billing history, and a suggested action. The human role shifts from discovery to judgment.
A 2024 BMC Medical Informatics paper on explainable unsupervised anomaly detection demonstrated an explainable ML workflow that flags atypical provider billing behavior and delivers the rationale to human investigators, enabling more efficient decisions without labeled fraud data.
AI does not remove human judgment from claim investigation. It removes the noise, so investigators can focus their expertise where it matters.
The RGA 2024 Survey found that only 45 percent of insurers conduct proactive fraud assessments on in-force portfolios. HITL routing solves this by making proactive assessment the default state rather than an exception.
Frequently Asked Questions About Claim Leakage in Health Insurance
What is the difference between claim leakage and insurance fraud?
Claim leakage includes both intentional fraud and unintentional overpayment from errors or system gaps. Fraud requires deliberate deception; leakage can occur without any intent, through billing mistakes, incorrect coding, or process failures. Both drain a TPA’s claims spend, but each calls for a different investigation and remediation approach.
What percentage of health insurance claims are affected by leakage?
Industry benchmarks place claim leakage at 5 to 10 percent of total annual claims spend for most health insurers and TPAs. For an APAC TPA managing $200 million in claims, that translates to $10 to $20 million in avoidable outflows. Detection rates vary sharply by leakage type and the maturity of the fraud detection system in place.
How does AI detect upcoding in health insurance claims?
AI detects upcoding by extracting the billed diagnosis and procedure codes from a claim and cross-referencing them against clinical documentation, expected cost benchmarks, and the provider’s historical billing patterns. When the billed code implies a cost that exceeds what the clinical notes support, the system flags the line item and routes it for human review before settlement.
Which health insurance fraud types are most common in India and Indonesia?
India’s primary fraud patterns are upcoded hospital bills in private cashless networks and inflated day-care procedure costs. Indonesia’s JKN program has documented phantom billing at affiliated hospitals, where services are billed without clinical evidence. Both markets also see prescription fraud, where drug quantities or off-formulary items appear in claims without matching prescriptions.
Can AI prevent claim leakage entirely without human reviewers?
No AI system eliminates claim leakage entirely without human review. The most effective designs use a two-gate AI pipeline that handles routine detection automatically and routes genuine anomalies to specialist investigators with a structured evidence pack. The human role shifts from volume processing to high-value judgment, which lowers both leakage and investigation cost simultaneously.
Three Priorities for TPA Leaders Building an Anti-Leakage Program
First, measure before you build. Most TPAs cannot quantify their leakage ratio. Run a retrospective audit on a closed claims sample to establish a baseline leakage rate by claim type and provider. Without this baseline, you cannot demonstrate ROI from any detection investment.
Second, sequence your gates correctly. Gate 1 completeness and document authenticity checks should be implemented before Gate 2 billing extraction and anomaly scoring. Gate 1 stops clean and complete submissions from becoming noisy edge cases at Gate 2. Sequence matters because the two gates solve different problems.
Third, design HITL routing for your investigators, not for your system. The output of Gate 2 is only as useful as the evidence pack it delivers. If your investigators receive a risk score without a structured explanation, they spend time reconstructing the case the AI already assembled.
Leakage that is not measured cannot be managed. Leakage that is not caught before settlement cannot be recovered.
These three steps create a sustainable anti-leakage capability rather than a one-time audit. As fraud patterns shift, including the growing use of AI-generated documents flagged in RGA’s 2024 survey, the gate architecture must evolve with them.
The question for every TPA COO reviewing this is not whether claim leakage exists in your portfolio. It does. The question is: at which gate in your current process does money leave that should not?
Table of Content